GitOps
Important
Refer to the Extended Config Schema (Recommended) to learn more about the parameters required to create an MKS Cluster via RCTL, Swagger v3 API, and GitOps System Sync.
GitOps System Sync facilitates bidirectional synchronization between the System (Rafay Controller) configuration and Git repositories. Any configuration changes made in the Git repository are reflected in the system (Rafay Controller), and vice versa. To learn more about System Sync, refer this page
This framework enables a 'GitOps' first approach for orchestrating operations by utilizing external triggers (Pipeline Triggers) for modifications made in Git and internal triggers whenever the artifact manifests in the Git repo need to be updated. With standardized specifications, managing configurations becomes extremely efficient.
Example
Below is an example of an extended specification for MKS Clusters used in system sync flow. The parameters included are:
- dedicatedControlPlane: Indicates that the control plane for the Kubernetes cluster should be dedicated. This means that specific nodes in the cluster are exclusively assigned to run the control plane components
- systemComponentsPlacement: Allows to configure the scheduling of system components on dedicated nodes. The functionality is now supported in RCTL, V3 APIs, and GitOps System Sync.
- cloudCredentials: These credentials are essential for enabling GitOps SystemSync functionality, providing the necessary authentication details for the GitOps Agent to interact with upstream Kubernetes cluster nodes, and have been integrated into the UI, RCTL, and SystemSync interfaces. SSH credentials, including the port, private key, username, and passphrase, are seamlessly integrated within the cloud credentials.
apiVersion: infra.k8smgmt.io/v3
kind: Cluster
metadata:
name: demo-mks
project: demo
spec:
type: mks
blueprint:
name: minimal
version: latest
cloudCredentials: mkscloudcreds
config:
autoApproveNodes: true
dedicatedControlPlane: true
kubernetesVersion: v1.29.4
location: sanjose-us
network:
cni:
name: Cilium
version: 1.14.1
podSubnet: 10.244.0.0/16
serviceSubnet: 10.96.0.0/12
nodes:
- arch: amd64
hostname: mks-node-1
operatingSystem: Ubuntu20.04
privateip: 10.0.0.106
roles:
- ControlPlane
- arch: amd64
hostname: mks-node-3
operatingSystem: Ubuntu20.04
privateIP: 10.0.0.207
roles:
- Worker
labels:
app: infra
taints:
- effect: NoSchedule
key: app
value: infra
systemComponentsPlacement:
nodeSelector:
app: infra
tolerations:
- effect: NoSchedule
key: app
operator: Equal
value: infra
Important
To use system sync functionality for MKS clusters, it is essential to use GitOps agents and cloud credentials created using these agents for upstream cluster types. Ensure that you update the GitOps agent to version r2.8.0 or later.
Create Cloud Credential¶
MKS Cloud credentials are crucial for enabling GitOps SystemSync functionality and have been integrated into the UI, and RCTL interfaces. They authenticate the GitOps Agent to interact with nodes in your upstream Kubernetes cluster.
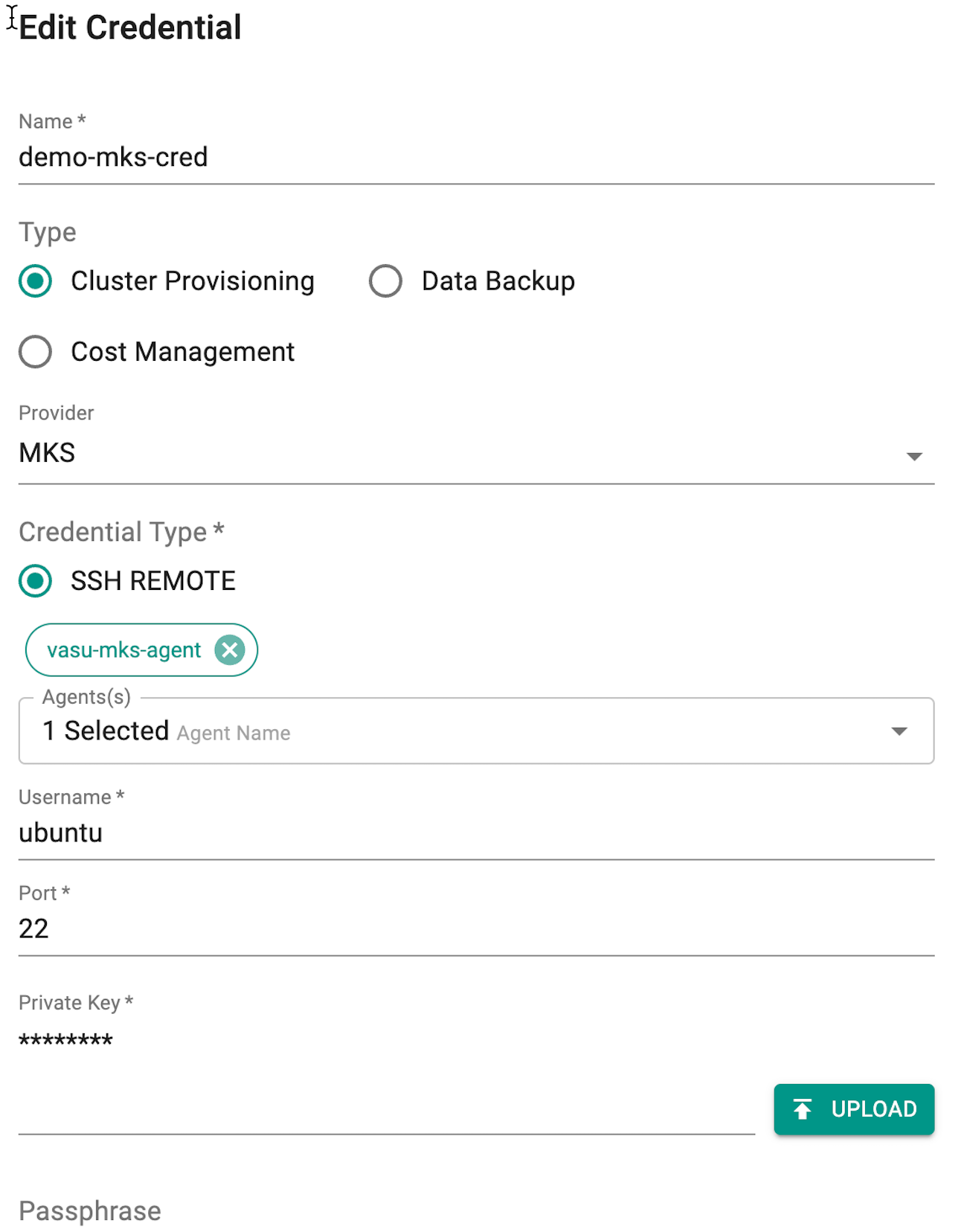
Follow the steps described below to create an IAM Role based cloud credential.
- Login to the Console and select "Cloud Credentials" under Infrastructure
- Click New Credential and provide a unique name
- Select the Type Cluster Provisioning
- Select provider MKS from the drop-down
- By default, the Credential Type is SSH REMOTE
- Select an Agent from the drop-down
- Provide
- Username to authenticate with the remote server or virtual machine where the MKS cluster will be provisioned,
- Port number on which SSH service is running on the remote server. The default SSH port is 22, but it can be configured to use a different port for security reasons.
- Private Key is a private SSH key associated with the SSH public key that is added to the authorized_keys file on the remote server. Users are allowed to upload the private key
- Optionally, add Passphrase to encrypt the private key
- Click Save
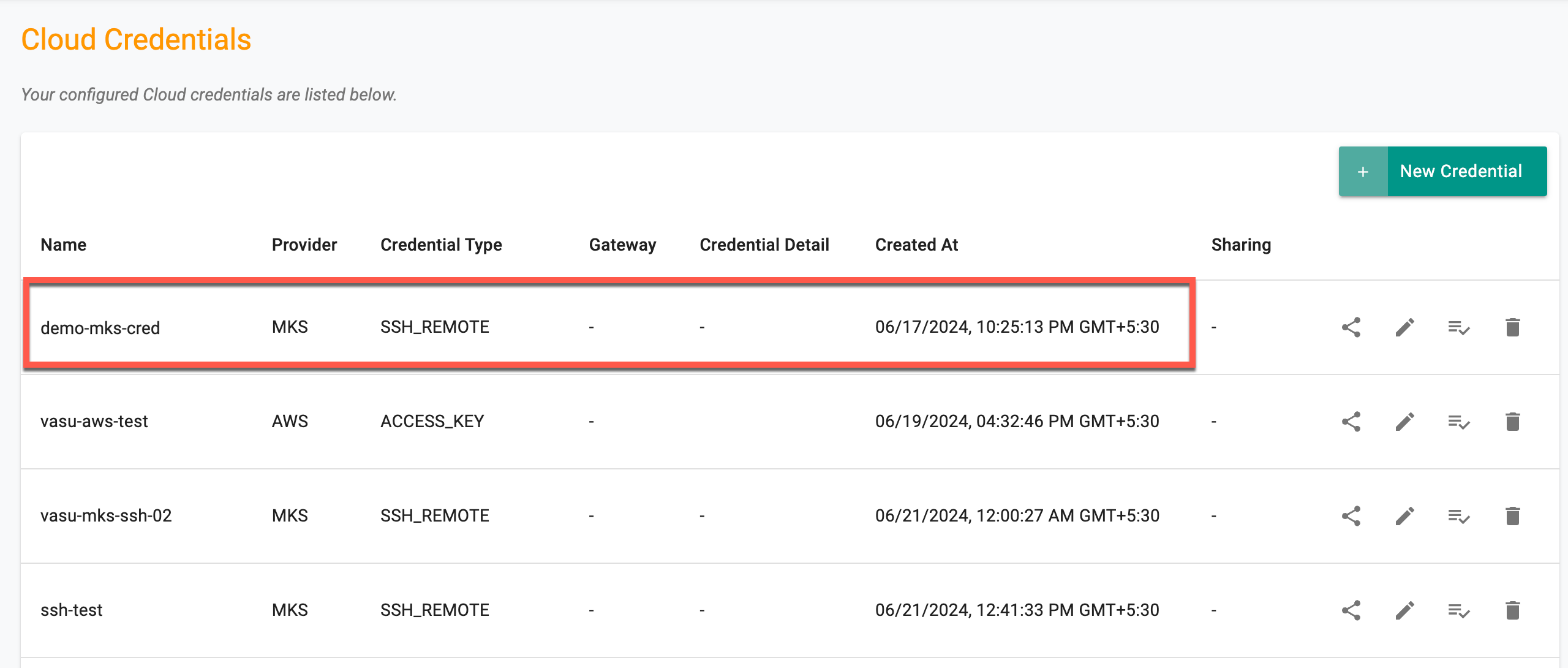
Once the credential is created, view it in the cloud credentials dashboard as shown below
Users can utilize these cloud credentials within the extended config specification to create a MKS cluster. Refer to the CLI for more details on the config spec and RCTL commands.
Refer to the Cloud Credentials page to create an MKS cloud credential via RCTL.
Managing Existing MKS Clusters Using GitOps¶
With the introduction of cloud credentials, it is now possible to manage existing MKS clusters using a GitOps system. Cloud credentials allow for streamlined management and orchestration of cluster configurations directly from a Git repository. Follow these steps to manage MKS clusters effectively with the GitOps framework.
Steps to Manage MKS Clusters¶
-
Ensure that the cluster is integrated with System Sync to enable bidirectional synchronization between the Rafay Controller configuration and Git repositories, allowing the GitOps system to keep the cluster configuration in sync with changes made in Git.
-
Add cloud credentials to the cluster configuration file to enable the cluster to access necessary cloud resources. Commit these changes to the Git repository, which triggers the pipeline to update the cluster configuration with the new cloud credentials.
spec:
blueprint:
name: default
version: latest
cloudCredentials: mks-cloud-creds
- Use the updated cluster configuration to perform additional operations as needed in the console.