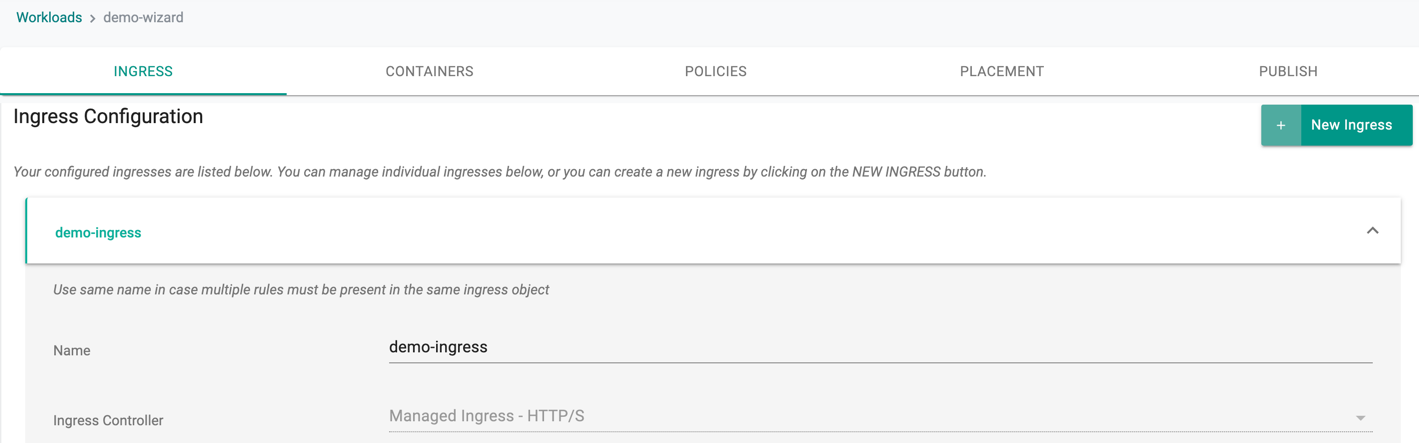
Ingress
Overview¶
Kubernetes supports a high level abstraction called Ingress that allows simple host or URL based HTTP routing.
Although an ingress is a core concept of Kubernetes, it is always implemented by a third party proxy. These implementations are known as ingress controllers. An ingress controller is responsible for reading the Ingress Resource information and processing that data accordingly. Different ingress controllers have extended the specification in different ways to support additional use cases.
The controller provides a "Managed Ingress Controller" option as part of the default blueprint and can be disabled by a customer per managed cluster if necessary.
NOTE: The "Managed" Ingress controller can be used by all types of workloads: "Helm", "Yaml" or "Workload Wizard.
Ingress Modes¶
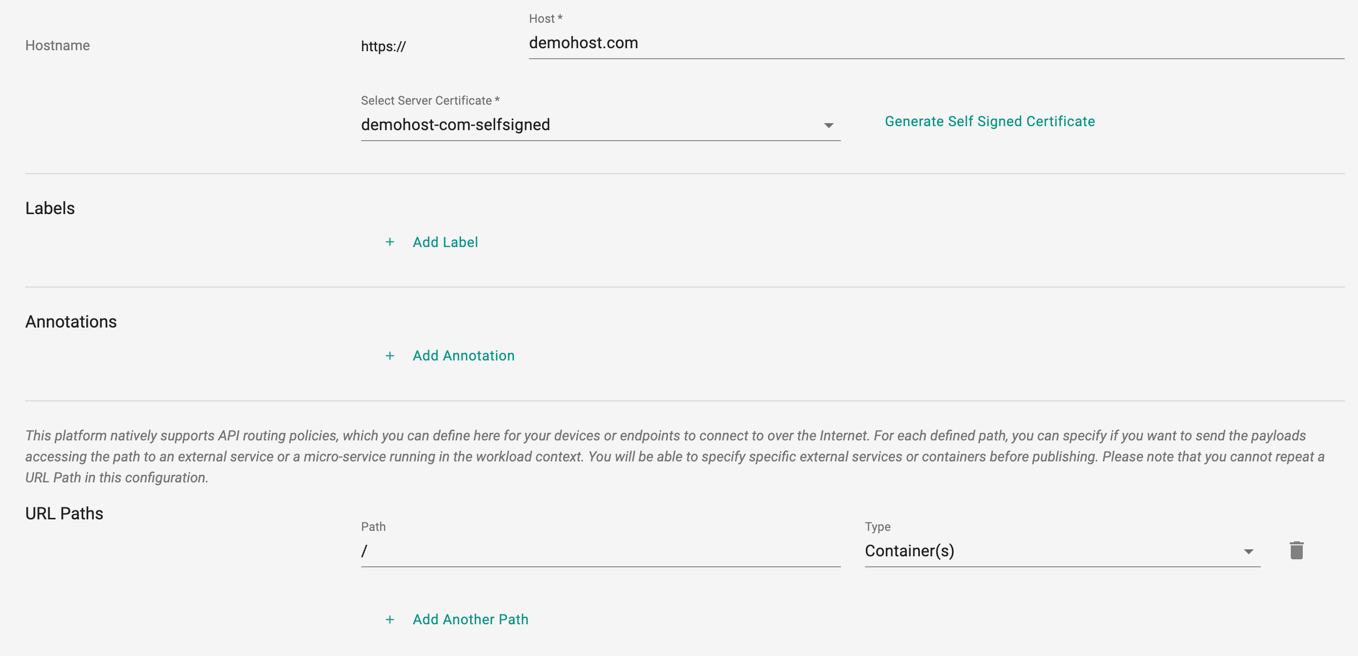
By default, the Ingress mode is supported for https traffic with the "managed" Ingress Controller.
| Mode | Description |
|---|---|
| Application Proxy | Requests terminated at Layer 7 |
Application Proxy Mode¶
Application Proxy mode helps for termination at the application layer (Layer 7) on the Ingress Controller.
This allows the developer to offload a number of burdensome, non-strategic tasks and helps them focus 100% on their core application logic.
When operated in this mode, the application can offload the following:
- Global Load Balancing
- Certificate Lifecycle Management
- Configure and Perform API routing
Multiple Ingress Policies¶
Multiple ingress policies can be configured for an application. For example, the same application may be accessible on the Internet on two different domains.