Overview
Overview¶
Istio is a popular service mesh with below functionalities:
-
Automatic load balancing for HTTP, gRPC, WebSocket, and TCP traffic.
-
Fine-grained control of traffic behavior with rich routing rules, retries, failovers, and fault injection.
-
A pluggable policy layer and configuration API supporting access controls, rate limits and quotas.
-
Automatic metrics, logs, and traces for all traffic within a cluster, including cluster ingress and egress.
-
Secure service-to-service communication in a cluster with strong identity-based authentication and authorization.
What Will You Do¶
In this exercise,
- You will create a cluster blueprint with "Istio" addon
- You will then apply this cluster blueprint to a managed cluster
Important
This tutorial describes the steps to create and use a Istio based blueprint using the Web Console. The entire workflow can also be fully automated and embedded into an automation pipeline.
Assumptions¶
- You have already provisioned or imported a Kubernetes cluster using the controller
Step 1: Create Istio addons¶
In this example we will be using Rafay's Catalog feature to install Istio addons.
- Login into the Web Console and navigate to your Project as an Org Admin or Infrastructure Admin
- Under Infrastructure, select "Namespaces" and create a new namespace called "istio-system"
-
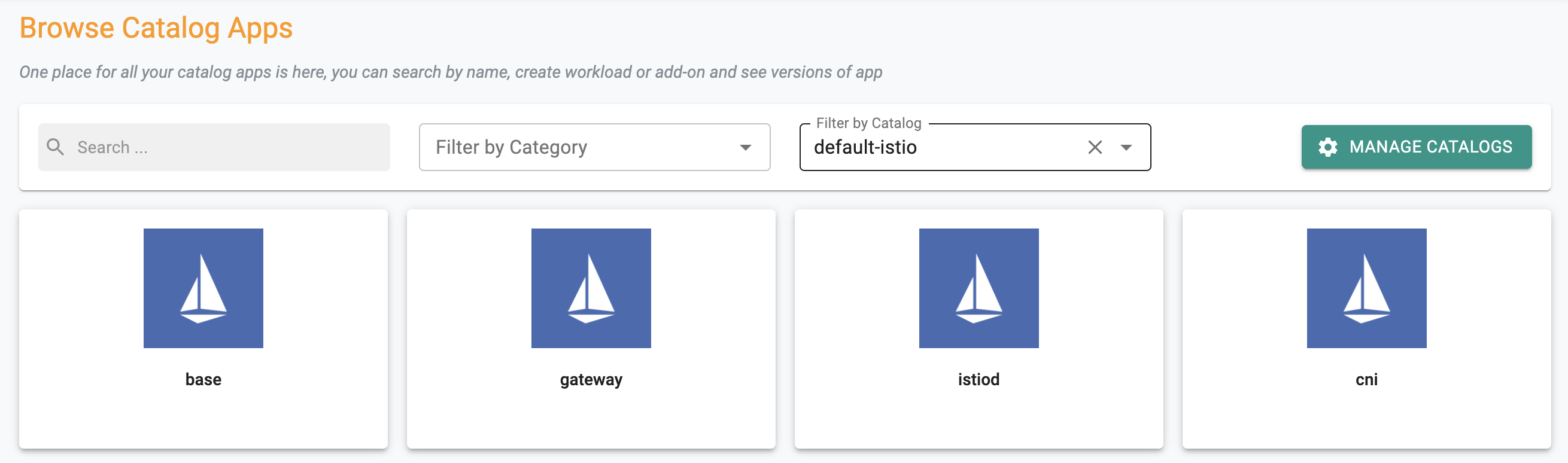
Navigate to Catalog and select "default-istio" from Filter by catalog. You should see istio components as below
-
Click on "base", select a stable version from top right and click "Create-Add-on"
- Give "istio-base" name and select the "istio-system" namespace that we created earlier. Click "Create"
- Give a suitable version number and click "Save Changes"
- Repeat the process for istiod and gateway addons with the same version selected with names "istiod" and "istio-gateway"
Step 2: Create Blueprint¶
Now, we are ready to assemble a custom cluster blueprint using this addon.
- Under Infrastructure, select "Blueprints"
- Create a new blueprint and give it a name such as "istio"
- Select "New Version" and give it a version name. Ex: istio-1.6.8
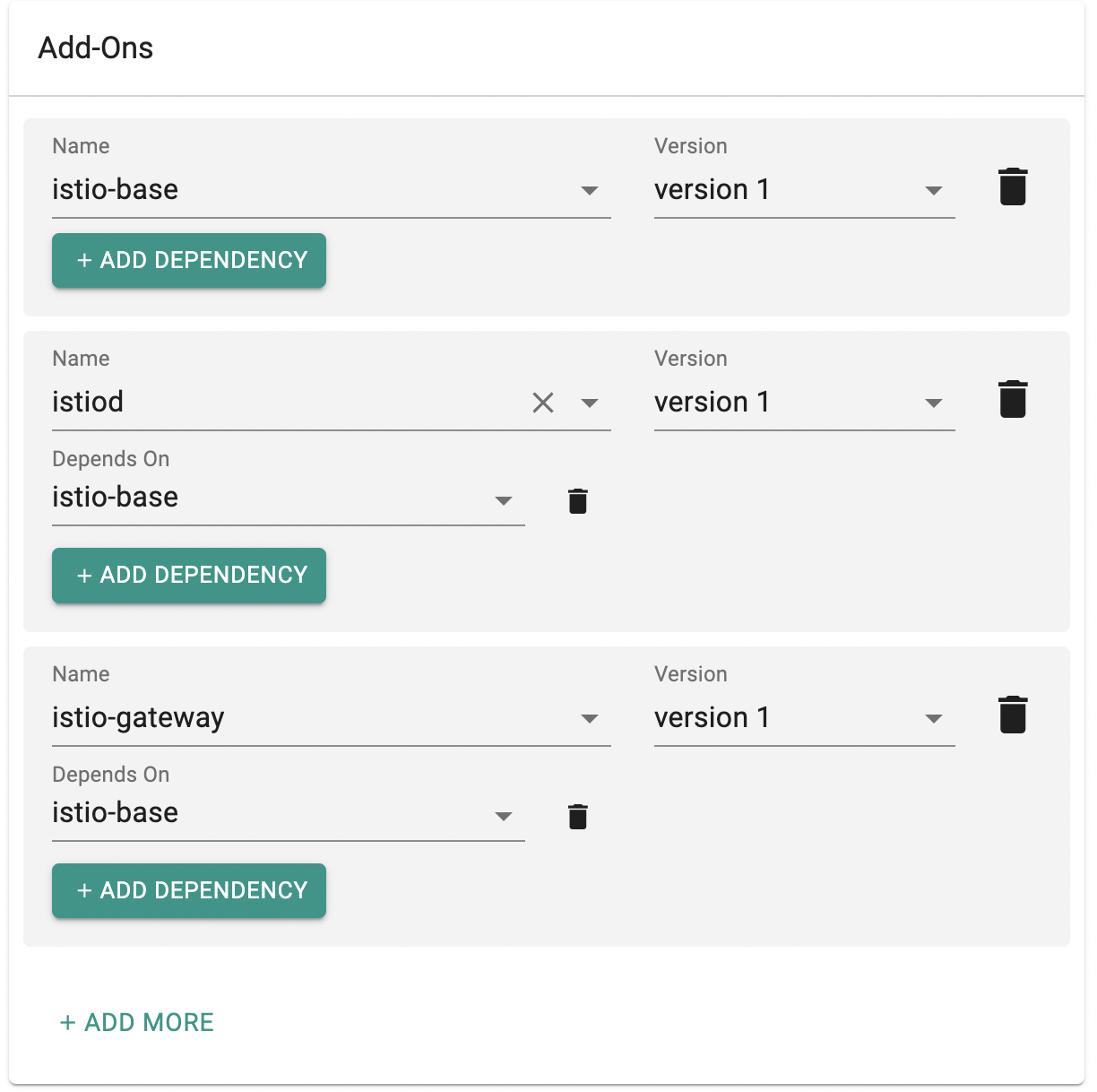
- Under Add-Ons, select "ADD MORE" and chose the "istio-base" addon created from Step 1.
- Add "istiod" and "istio-gateway" in the same way.
- You need to add a dependency for istiod and istio-gateway as they both are dependent on istio-base to be istalled first. Click "Add Dependency" below istiod and istio-gateway and select istio-base as dependency.
- Click "Save Changes" to save the blueprint.
Step 3: Apply Blueprint¶
Now, we are ready to apply this blueprint to a cluster.
- Click on Options for the target Cluster in the Web Console
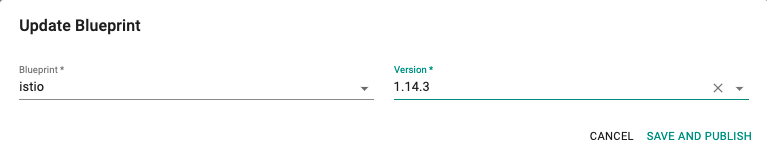
- Select "Update Blueprint" and select the "istio" blueprint from the dropdown and for the version select "istio-1.14.3" from the dropdown.
- Click on "Save and Publish".
This will start the deployment of the addons configured in the "istio" blueprint to the targeted cluster. The blueprint sync process can take a few minutes. Once complete, the cluster will display the current cluster blueprint details and whether the sync was successful or not.
Step 4: Verify Deployment¶
Users can optionally verify whether the correct resources have been created on the cluster.
- Click on the Kubectl button on the cluster to open a virtual terminal
First, we will verify if the istio-system namespace has been created
kubectl get ns istio-system
Next, we will verify if the pods are healthy in the "istio-system" namespace
kubectl get po -n istio-system
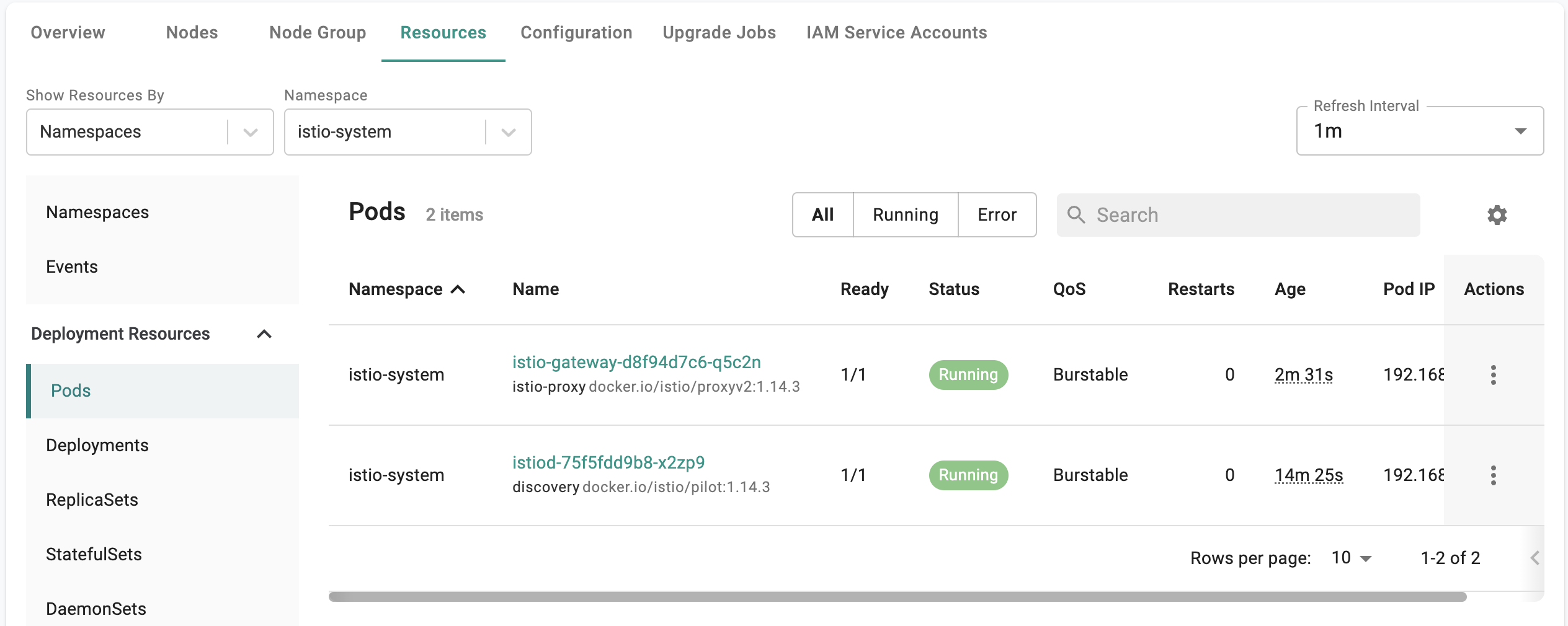
NAME READY STATUS RESTARTS AGE
istio-gateway-d8f94d7c6-q5c2n 1/1 Running 0 3m
istiod-75f5dd9b8-x2zp9 1/1 Running 0 15m
Optionally you can check from Rafay console by navigating to the cluster > Resources > Istio-system namespace > Pods
Recap¶
Congratulations! You have successfully created a custom cluster blueprint with the "istio" addon and applied to a cluster.